October 7, 2021
Cyber attacks that steal data and wreak havoc on organizations of all sizes and types are so common these days that it’s no longer a matter of if but when a business will be impacted.
That’s why it’s more crucial than ever to implement an effective cybersecurity framework, defined by Mishaal Khan, Mindsight’s cybersecurity leader and virtual CISO as “guidance for internal and external stakeholders that includes processes, best practices, and technologies which companies use to manage their cybersecurity risk.”
Which framework — since there are many — depends on your organization’s specific needs.
At Mindsight’s hybrid event on October 14 titled “Building a Secure Foundation for Your IT Infrastructure,” Khan, alongside Mindsight CIO Tad Gralewski— will discuss two foundational frameworks that are widely adopted and feature comprehensive security controls: CIS and NIST. In doing so, they’ll cover:
- Elements of a solid cybersecurity strategy
- How to assess and prioritize risk to your organization
- Cybersecurity frameworks: NIST vs CIS
- The case for security investment and getting C-Level buy-in
We’ll tee things up here by defining what CIS and NIST are, and why they’re important.
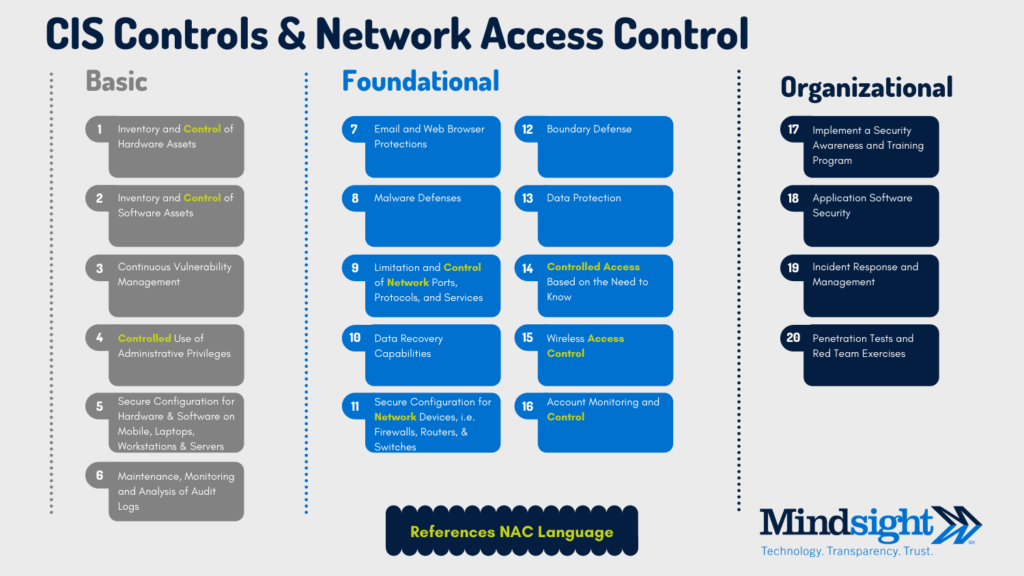
CIS CONTROLS (version 8)
What it is: Developed and maintained by the independent, nonprofit Center for Internet Security, CIS, formerly the CIS20, lays out best practices (aka “cyber hygiene”) for developing cybersecurity programs at a reasonable cost. The controls were updated earlier this year to keep up with modern systems and software. Remote work, the result of the pandemic, combined with more outsourcing, virtualization, moving workloads to the cloud, and increasingly complex cyberattacks prompted the Center for Internet Security to update the framework. According to Khan, “The shift to hybrid cloud environments as well as “fully cloud” environments has in many ways increased risk exposure for companies. Updating the CIS controls for today’s modern workforce will help companies prevent and protect against some of the most dangerous and pervasive threats out there.”
What it does: CIS’s official mission is “to develop, validate, and promote timely best practice solutions that help people, businesses, and governments protect themselves against pervasive cyber threats.” In addition to globally recognized CIS Controls, companion guides, and mappings, the organization provides over 100 configuration guidelines for a wide variety of vendor products.
NIST (National Institute of Standards and Technology)
What it is: NIST stands for National Institute of Standards and Technology. Founded in 1901, NIST is a non-regulatory federal agency within the U.S. Department of Commerce. Adhering to the NIST framework is required for all Department of Defense contractors. Part of its role — as assigned by the Cybersecurity Enhancement Act of 2014 — is to identify and develop “cybersecurity risk frameworks for voluntary use by critical infrastructure owners and operators.”
What it does: NIST’s five main functions are to identify, protect, respond and recover. Used by many midsize to enterprise-size organizations, it’s charged with identifying “a prioritized, flexible, repeatable, performance-based, and cost-effective approach.” There are many variations and derivatives of this standard created by local agencies to suit their specific requirements.
“While adopting a security standard to create a roadmap may seem daunting at first,” Khan says, “it’s an essential step towards creating a secure environment.” Many organizations, especially those lacking cybersecurity expertise in-house, are turning to virtual chief information security officers (vCISOs) to augment this critical skills gap. Khan, a vCISO, helps clients adopt security standards such as CIS and NIST, and develops roadmaps to improve security posture and protect against the biggest threats. Mindsight’s vCISO can be as involved as needed, becoming an extension of your IT team.
About Mindsight
Mindsight is industry recognized for delivering secure IT solutions and thought leadership that address your infrastructure and communications needs. Our engineers are expert level only – and they’re known as the most respected and valued engineering team based in Chicago, serving emerging to enterprise organizations around the globe. That’s why clients trust Mindsight as an extension of their IT team.
Visit us at http://www.gomindsight.com.
About The Experts
Mindsight CIO/COO Tad Gralewski is graduate of the University of Illinois at Champaign-Urbana and has been in the IT industry for over three decades. At Mindsight, Tad focuses on both delivering Mindsight’s services to our customers and working with them to help develop strategies, roadmaps, and solutions to solve their issues. To Tad, “We don’t sell things – we solve problems”. A self-proclaimed “outdoors person”, Tad enjoys camping, hiking, and riding motorcycles in his spare time.
Mishaal Khan, Mindsight’s Security Solutions Architect, has been breaking and – thankfully – rebuilding computers for as long as he can remember. As a Certified Ethical Hacker (CEH), CCIE R&S, Security Practitioner, and Certified Social Engineer Pentester, Khan offers insight into the often murky world of cybersecurity. Khan brings a multinational perspective to the business security posture, and he has consulted with SMBs, schools, government institutions, and global enterprises, seeking to spread awareness in security, privacy, and open source intelligence.
