July 11, 2024
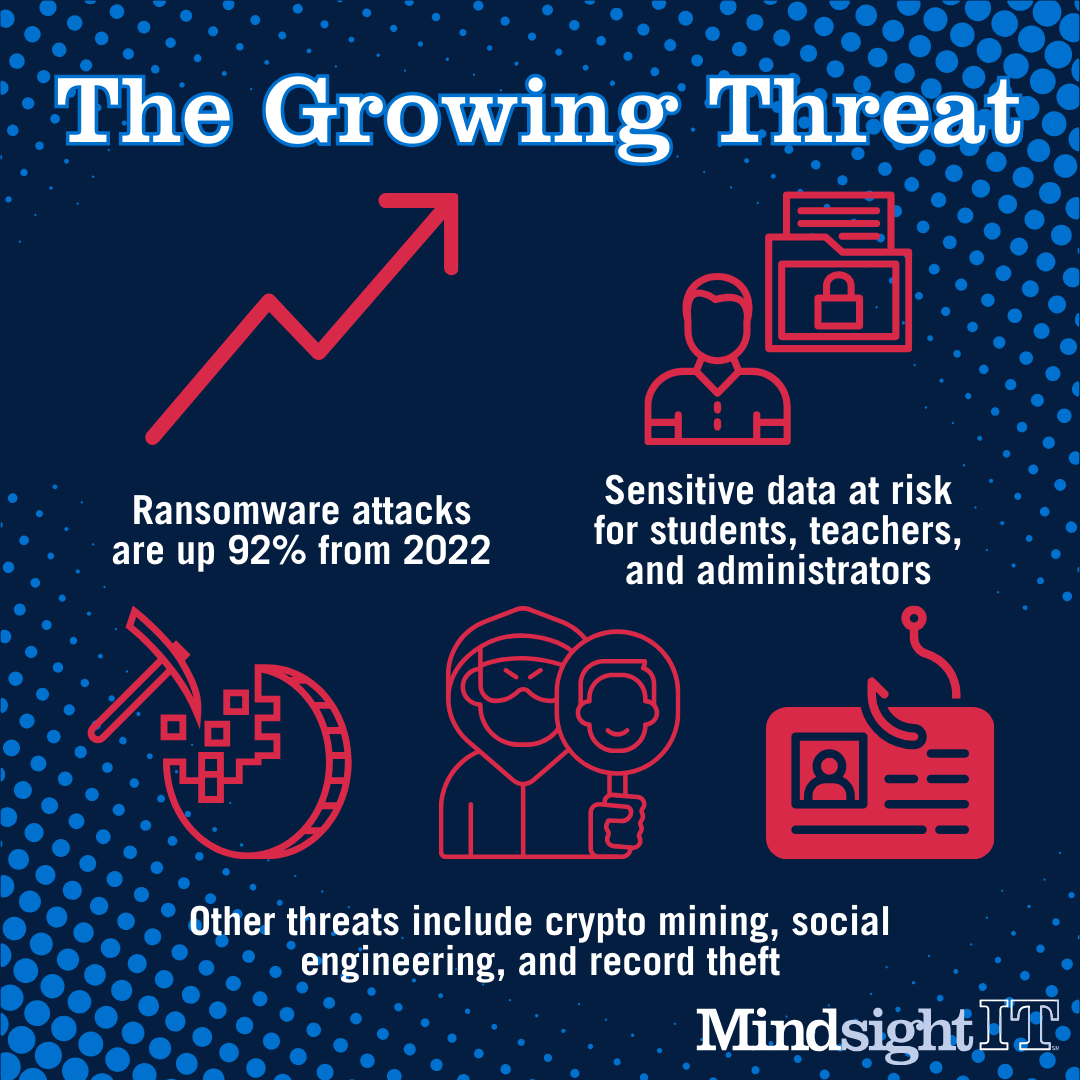
Last year was a record one for ransomware attacks against K-12 schools. Up 92 percent from 2022, they jeopardized highly sensitive data and put students, parents, teachers and administrators at risk.
“It’s not just ransomware, though,” a recent Forbes article noted. “School districts are prime targets for crypto mining operations, social engineering schemes and student record theft, which includes student information alongside sensitive, identifiable information on parents, medical histories and more.”
According to experts, 2024 looks no less bleak. Despite various initiatives, including on the part of the federal government, to strengthen cybersecurity in schools across the nation, they remain easy targets.
“While it’s hard to know exactly how many K-12 school systems have been targeted by hackers,” a 2024 NPR write-up revealed, “an analysis by the cyber security firm Emsisoft estimates that 45 school districts were attacked in 2022. In 2023, Emsisoft found that number more than doubled, to 108.”
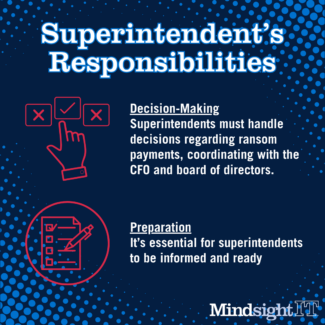
Addressing the problem in substantive ways is no simple matter, but those in the know say it needs to involve key school personnel—beginning with superintendents.
Mindsight’s cybersecurity lead, Mishaal Khan, recently hosted a security seminar for superintendents in which he detailed the increasingly dire threat landscape they face, outlined a host of protective measures and guided them through some exercises that mirrored real-world scenarios.
“My main takeaway,” he says, “was they are not prepared.”
That’s generally the case nationwide. But it doesn’t have to be.
“Everyone knows why we should be secure,” he adds. “But when it really happens to them, when they’re put on the spot, there are so many things they don’t realize.”
Here are Khan’s expert suggestions for bolstering K-12 cybersecurity to guard against increasingly common and sophisticated attacks.
Not an IT problem
If you get hacked and IT systems are still up and running, it’s not an IT problem. Say somebody transferred $50,000 to the wrong vendor. That’s a hack, but it’s not an IT problem. Or maybe somebody stole lots of data—sensitive student and health records—but systems are still up and running. Again, that is not an IT problem as would be, for example, a backup disaster recovery situation. So now you need to decide, “Should we pay the ransom?” An IT director will not decide that. The CFO and the board of directors and, in school systems, superintendents will decide that. If the answer is, “Yes, we’ll pay it,” do you have the Bitcoin to do so? Will your insurance help you in paying part of the ransom? Again, this is not an IT problem. Superintendents and those they work with need to know all that stuff ahead of time. Technology can help, but it’s never—or shouldn’t be—the first line of defense.
The most common threat
Social engineering will always be the largest threat against schools and other organizations, because it’s such a broad attack surface to exploit. Social engineering is basically fooling the mind, hacking humans. And in most of these scenarios, the attacker doesn’t hack a system, they hack a process. It could be an HR process, an accounting process, a PR process. Of course, they’re using technology to do it: voice cloning, number spoofing, phishing emails. They may even pretend to be someone else via phone or video—or by showing up physically. And even though they’re using technology to do most of these things, they’re exploiting humans.
Third-party attacks
Most recent attacks were related to third parties. The school district wasn’t attacked directly. Instead, one of the hundreds of vendors that had access to their systems was compromised. Which means they were indirect attacks, or proxy attacks. In the Raptor Systems attack reported early this year, attackers breached 4 million student records from multiple school districts. Raptor Systems provides the physical security for these schools, but they were ingesting more data than they should have from students, parents and others. Health records, records of security cameras that didn’t work. There were a lot of physical security-based leaks in that hack. One of the lessons was that, yes, we need third party vendors, but give them only enough access to perform their duties—nothing more, nothing less.
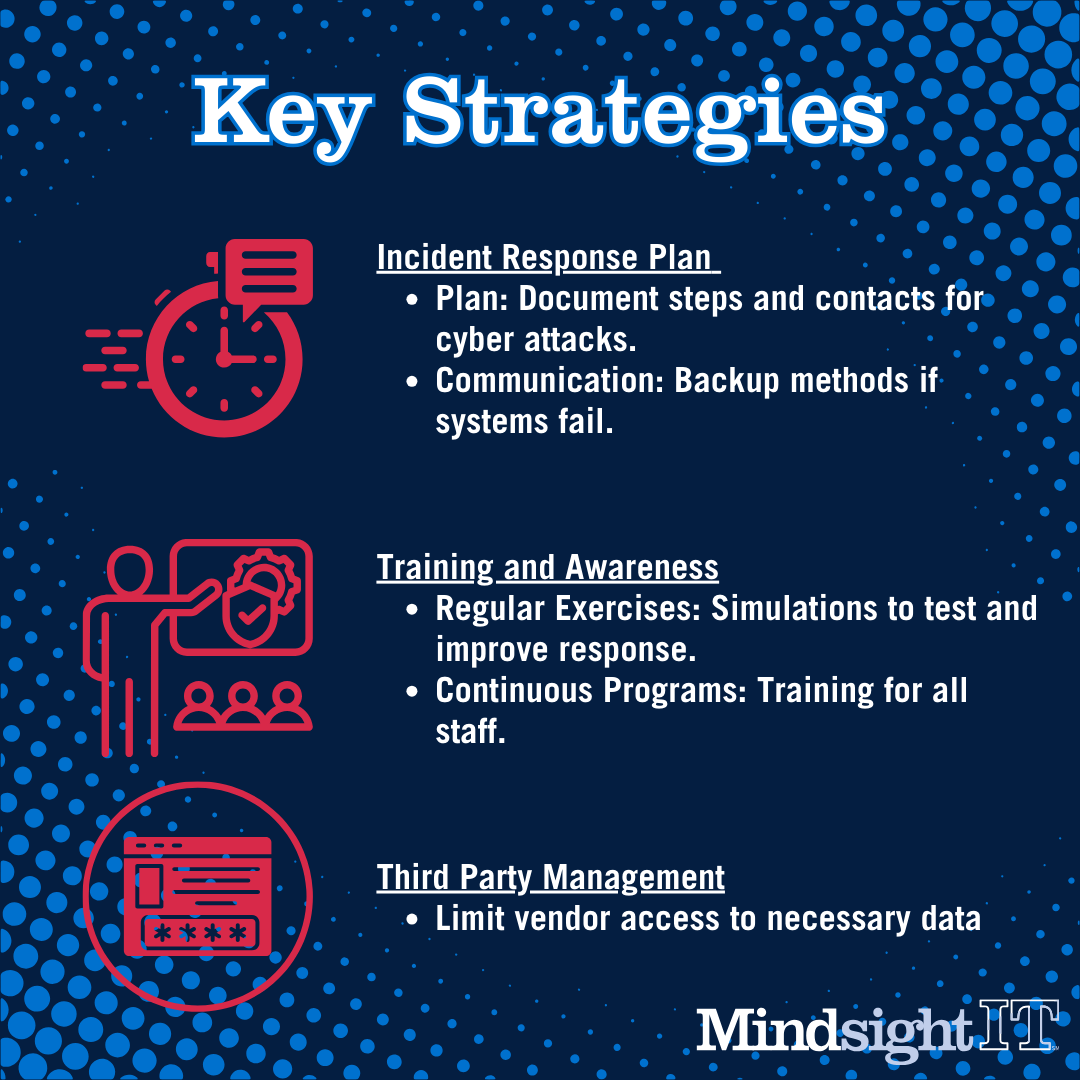
Creating priorities
The number one way to be prepared is incident response planning. Have a plan in place, which means a physical document that shows the steps to take in the event of an attack. Who do you call? What communications methods should you use? If your systems are down and your Microsoft Teams or WebEx won’t work, what is your alternate means of communication? Once you have a plan of action, begin playing it out in regular training exercises to test the effectiveness of your system, processes and protocols. That’s how you identify and patch vulnerabilities. If new technology is introduced, make sure it’s in the service of heightening human awareness. That means security awareness-based training programs, as well as digital and logging tools that monitor data and usage. There should also be EDR, MDR or SOC services, where a third party is monitoring your security presence. Cyber insurance is another consideration, so you’re covered financially, but that’s way down on your list of priorities.
Key players involved
Partners need to work hand in hand, because one of the major issues in school districts across the country is low budgets and lack of resources. That’s a gap that can easily be fulfilled by managed service providers, which are key for school districts—most of which can’t hire full-time experts. The MSP model also works well when it comes to handling hundreds, if not thousands, of vendors. It’s just too much work to keep an eye on what’s coming in and what’s going out, particularly for non-tech people who have little or no security training. It’s why check fraud and business email compromise are so common in school districts. They have a barrage of vendor activity, and no one’s really managing those vendors to determine; Are they old or new? Is this transaction fraudulent or legit?
Ultimately, Khan says (repeating a favorite refrain): It’s all about training and awareness. Knowing what could happen and how to proceed if it does happen (because chances are good something will happen) is the only way to keep sensitive data—and, most important, people— safe.
About Mindsight
Mindsight, a Chicagoland IT services provider, is an extension of your team. Located in Downers Grove, IL we proudly serve customers across the area including Naperville, Oak Brook, Northbrook, and surrounding counties (Cook, Lake, Dupage, Will, Kane, and Grundy). Our culture is built on transparency and trust, and our team is made up of extraordinary people – the kinds of people you would hire. We have one of the largest expert-level engineering teams delivering the full spectrum of IT services and solutions, from cloud to infrastructure, collaboration to contact center. Our highly certified engineers and process-oriented excellence have certainly been key to our success. But what really sets us apart is our straightforward and honest approach to every conversation, whether it is for an emerging business or global enterprise. Our customers rely on our thought leadership, responsiveness, and dedication to solving their toughest technology challenges.
About The Expert
Mishaal Khan is a subject matter expert in cybersecurity, pentesting, privacy, Open-Source Intelligence, and social engineering. He is a frequent speaker on these topics at universities and popular cybersecurity conferences like DEFCON, Wild West Hacking Fest, and multiple BSides events. Mishaal has worked with multinational companies for over 20 years, securing their networks and providing executive-level consultancy to manage risk and avoid breaches. He’s an author, holds a CCIE and CEH, and runs the cybersecurity practice at Mindsight as a vCISO. Visit Mishaal’s LinkedIn page.