Updated September 1, 2020 by Siobhan Climer and Mishaal Khan
Security threats in the workplace are ever-present. Cyber criminals are a bit like the dinosaurs in Jurassic Park; they are constantly testing the defenses, searching for a weak spot. When that weak spot appears – say a sudden influx of people working from home resulting in massive remote scale workforce deployments – criminals are ready to act.
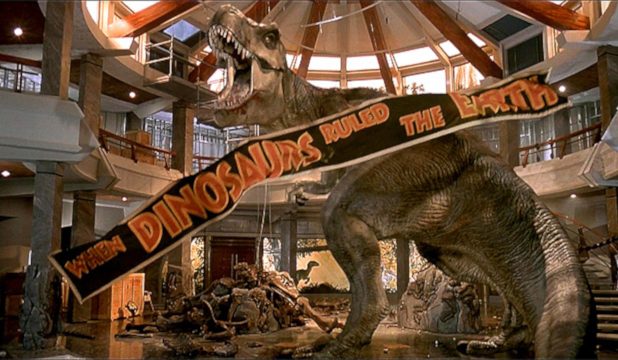 Like the Jurassic Park dinosaurs, though, the threats can emanate from within. While there are increasing risks from outsiders, insiders – whether through negligence or malicious intent – are also at risk of breaching security defenses. In the 2020 Cost of Insider Threats report by the Ponemon Institute and ObserveIT, they reported the average cost of insider threat damage equaled $11.45 million. That’s up 31% from $8.76 million in 2018. The number of incidents increased by 47%.
Like the Jurassic Park dinosaurs, though, the threats can emanate from within. While there are increasing risks from outsiders, insiders – whether through negligence or malicious intent – are also at risk of breaching security defenses. In the 2020 Cost of Insider Threats report by the Ponemon Institute and ObserveIT, they reported the average cost of insider threat damage equaled $11.45 million. That’s up 31% from $8.76 million in 2018. The number of incidents increased by 47%.
Finally, to take the Jurassic Park dinosaur analogy to its conclusion, cyber criminals are prepared to evolve to changes in the environment. The dramatic shift to remote work provides a new set of variables insiders are capable of exploiting.
The insider threat – like nature – always finds a way.
What Is An Insider Threat?
The “insider threat” typically refers to employees or third-party contractors. These individuals have established credentials that can, in the right circumstances, enable them to move laterally and virtually undetected within a defense network.
Organizations across the globe worry about the cybersecurity insider threat. 68% of businesses report being vulnerable to insider attacks, according to the 2020 Insider Threat Report by Gurucul.

Other insights in the report found:
- 53% of organizations believe detecting insider attacks has become harder since migrating to the cloud
- 31% cite lack of resources and 22% cite false positives as the biggest hurdles in maximizing SIEM value
- Only about one third of organizations can detect anomalous behavior in NetFlow/packet data, service accounts, and cloud resources
- 63% of organizations think that privileged IT users pose the biggest insider security risk
Their concern mirrors reality. 57% of database breaches come from inside the company, according to the Verizon Insider Threat Report. In the 2016 IBM Index Report, 75% of internal attacks were intentional and 25% were the result of phishing.
Whether an employee uses their credentials to damage the business (or offers those credentials to a hacker) or mistakenly clicks a malicious link, employees are one of the top cybersecurity threats to any organization.
What Makes The Insider Threat In Remote Work Environments Unique?
The current work environment, which has been deeply impacted by current lay-offs and most employees working from home, means businesses have moved their employees to remote work or work-at-home policies. The mandate back in March came swiftly, and for many businesses, cybersecurity concerns were forced to take a back seat during the transition.
 Threat actors were watching. To take advantage of this shift, cyber criminals have adapted their methods, focusing on sophisticated phishing campaigns and data exfiltration. Both exploit credentialed users. The latter is especially critical at this phase, as criminals use privileged access to move data within (and out of) the network.
Threat actors were watching. To take advantage of this shift, cyber criminals have adapted their methods, focusing on sophisticated phishing campaigns and data exfiltration. Both exploit credentialed users. The latter is especially critical at this phase, as criminals use privileged access to move data within (and out of) the network.
At the same time, the network is now distributed. The natural perimeter established by a physical environment has evaporated – and fast.
For CISOs and CIOs, it is critical that not only do you employ a robust security framework (i.e. NIST or the CIS20), you must also take a proactive approach to ensuring that however the work environment changes going forward, attackers can’t get in and insiders can’t get data out.
Protecting Against The Insider Threat
It’s not hopeless, though. While riding off in a helicopter isn’t an option, there are proactive measures you can take to protect against the cybersecurity insider threat brought on by a remote work deployment:
- Take Care Of Your Employees – Satisfied, empowered users are less prone to threaten their employer. Provide a human, empathetic culture. Communicate with transparency and help educate them on cybersecurity hygiene. And remember – even CISOs and cybersecurity pros can be fooled by a sneaky cyber criminal. Note: Disgruntled employees are an enormous threat to security. We’re looking at you, Dennis Nedry.
- Pay Attention And Use Your Tools – Monitor the network, understand what users are doing and what they are accessing. Be especially cognizant of your data vaults. And, wherever possible, shift any human focus to the most high-risk and probable scenarios.
- Be Ready To Respond – Most businesses today have been breached in one manner or another. It’s pervasive. Be ready to respond with conviction and action, taking away important lessons and communicating them to stakeholders. Criminals thrive on indecisiveness and uncertainty.

Start Your Insider Threat Watch With Data
 “You don’t know what you don’t know,” Mishaal Khan, Senior Security Solutions Architect at Mindsight says. Be prepared for the insider threats that threaten your network by starting with a complete deck of data. Mindsight can help with a service to match your cybersecurity needs and level of security sophistication.
“You don’t know what you don’t know,” Mishaal Khan, Senior Security Solutions Architect at Mindsight says. Be prepared for the insider threats that threaten your network by starting with a complete deck of data. Mindsight can help with a service to match your cybersecurity needs and level of security sophistication.
And remember: if there’s one place where one should “spare no expense”, it’s cybersecurity.
- Testing and Analysis
- Program Assessment and Compliance
- Incident Response and Digital Forensics
- Remediation and Controls
Like what you read?
Contact us today to discuss the insider threat and cybersecurity.
About Mindsight
Mindsight is industry recognized for delivering secure IT solutions and thought leadership that address your infrastructure and communications needs. Our engineers are expert level only – and they’re known as the most respected and valued engineering team based in Chicago, serving emerging to enterprise organizations around the globe. That’s why clients trust Mindsight as an extension of their IT team.
Visit us at http://www.gomindsight.com.
About The Authors
Mishaal Khan, Mindsight’s Security Solutions Architect, has been breaking and – thankfully – rebuilding computers for as long as he can remember. As a Certified Ethical Hacker (CEH), CCIE R&S, Security Practitioner, and Certified Social Engineer Pentester, Khan offers insight into the often murky world of cybersecurity. Khan brings a multinational perspective to the business security posture, and he has consulted with SMBs, schools, government institutions, and global enterprises, seeking to spread awareness in security, privacy, and open source intelligence.
Siobhan Climer writes about technology trends in education, healthcare, and business. With over a decade of experience communicating complex concepts around everything from cybersecurity to neuroscience, Siobhan is an expert at breaking down technical and scientific principles so that everyone takes away valuable insights. When she’s not writing tech, she’s reading and writing fantasy, hiking, and exploring the world with her twin daughters. Find her on twitter @techtalksio.


